BLOG
 Electronic Security
Electronic Security
Integrated Security Solutions: The “Single Pane of Glass” (SPOG) Approach
A longstanding trend in security has been the pursuit of a unified, user-friendly overview of an organization’s security systems—without forcing practitioners to juggle multiple platforms, clients, or applications. This “single pane of glass” (SPOG) capability has long been available to large enterprises, such as Fortune 1000 companies, through advanced Physical Security Information Management (PSIM) software. […]
 Cash Automation
Cash Automation
Measuring What Matters: How Wittenbach Achieved 91.26% Customer Satisfaction Through Operational KPIs
In service-driven industries, customer satisfaction is often discussed—but rarely measured in a way that reflects the full operational reality behind it. At Wittenbach, we believe performance should be transparent, measurable, and tied directly to the outcomes our customers experience every day. That belief led us to develop an internal customer satisfaction measurement framework built directly […]
 Cash Automation
Cash Automation
Recommended BIOS Security Update to Help Prevent ATM Jackpotting Attacks
Strengthening ATM Protection Against Emerging Threats ATM jackpotting attacks continue to evolve, targeting vulnerabilities in both physical hardware and internal system configurations. To help financial institutions stay ahead of these threats, Hyosung Americas has issued a new security recommendation designed to further protect ATM fleets from unauthorized access and exploitation. As a long-standing provider of […]
 Electronic Security
Electronic Security
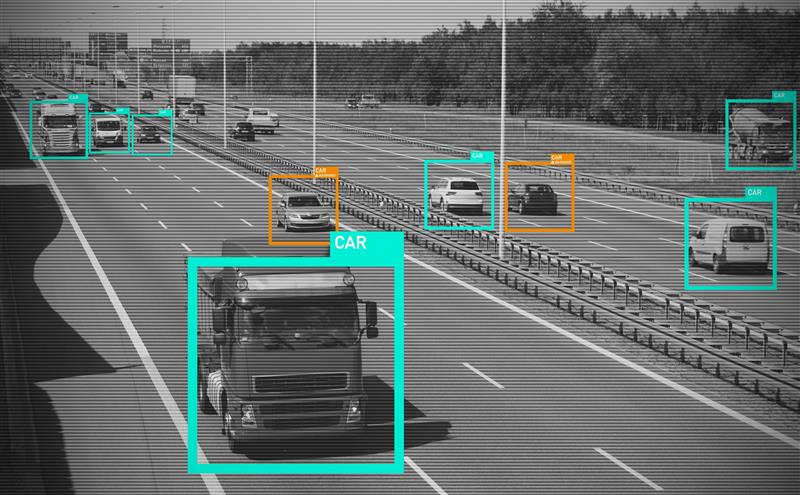
Artificial Intelligence in Video Security: Practical Paths to Implementation
Artificial intelligence (AI) continues to dominate industry discussions – and for good reason. In a recent Wittenbach blog article, AI in Security Video Surveillance (https://wittenbach.com/ai-in-security-video-surveillance/), we explored the topic at a high level. That overview provides helpful context and is worth reviewing before diving deeper. This article focuses more narrowly on where AI is delivering […]
 Managed Services (FI)
Managed Services (FI)
Wittenbach: Enhancing Bank Security and Compliance in the Modern Branch
Banking has undergone a major shift over the past decade. Branches have transitioned toward open layouts, universal bankers, and customer-first experiences that minimize physical barriers between staff and visitors. This strategic shift improves service and visibility — but it also introduces new security and compliance challenges. While branch formats have evolved, many institutions still rely […]