Electronic and physical security are two of Wittenbach’s main foundational pillars; our in-house experts and industry partners are leaders in branch security. Access control is one important measure to keep your employees, clients, and assets safe both during and outside business hours. The access control arena is a point of significant innovation in recent years, evolving from in-person controls to nearly full mobile capabilities.
Below, we will outline the components of an access control system, strides the industry has made to optimize functionality, and products that Wittenbach stands behind to supplement your financial institution’s physical security efforts.
What is access control?
Access control systems “grant access to employees and contractors who work at or visit a site by electronically authenticating their […] credentials,” says FICAM Architecture. Although they are part of an IT landscape, they must be designed, installed, and maintained in conjunction with the broader branch or business’s electronic and physical security infrastructure. Access control systems can guard zones or your entire building, and are applicable in industries from the financial sector to hospitals, government buildings, schools and campuses, pharmacies, and anywhere in which a heightened level of asset and employee security is required. In a bank or credit union, not only can control the main entryway to the building, but it can control access to a safe room, and also access for cash-in-transit (CIT) deliveries to specific zones of the building.
Broken down into its basic parts, an access control system is comprised of the following elements, per OpenPath:
- An access point, where the barrier to entrance is situated. “Common physical access control examples of access points include security gate systems, turnstiles and door locks. A secure space can have a single access point, like an office inside a larger complex, or many access points.”
- Personal credentials are required to enter the access point. Credentials may be provided to some or all employees in the form of a code or an identification badge with chip. Other systems may require biometric readings such as fingerprint, face, or retina scans. Modern access control systems audit times and locations of entries and exits, providing reporting that can spot trends in the event of suspicious activity or a breach.
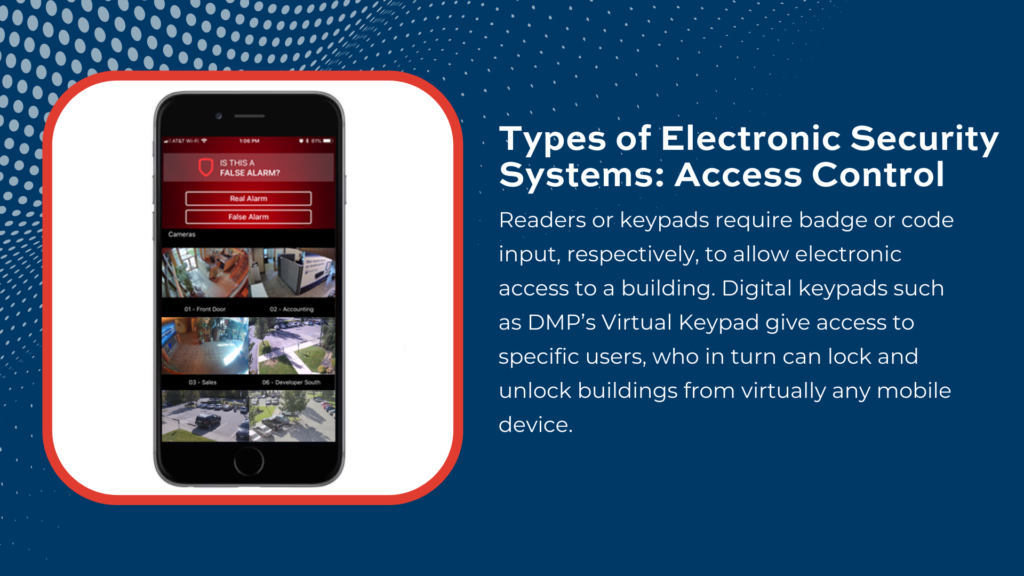
- Readers or keypads require badge or code input, respectively, to allow electronic access to a building. The more traditional, older models of these devices were affixed to the building itself. However, digital keypads such as DMP’s Virtual Keypad give access to specific users, who in turn can lock and unlock buildings from virtually any mobile device.
- A control panel accepts information from the reader, determining whether access should be permitted or denied. If denied, the end user will not be permitted to enter the branch or building, unless the access control system allows for a certain number of available retry attempts.
- Access control server: Dicsan Technology explains, “Every access control system needs a server where the permissions are stored in an access control database. As such, it acts as the center or “brain” of the access control system. The server decides if the doors should unlock by matching the presented credential to the credentials authorized for this door. The access control server base tracks and records activity and events regarding access and pulls reports of past data events for a given period.”
Access control systems may also be integrated with monitoring services, fire alarms, and other surveillance products. Virtual aspects, such as the DMP Virtual Keypad, signify advancements in access control technology; other systems also use biometrics instead of a keypad, capturing finger or palm prints, voice, or iris scans to allow entry. According to BeStructured Technology Group, there are three main types of access control systems:
- Discretionary Access Control (DAC): One main administrator gives access to specific employees and contractors within their company. This could be certain zones of a branch, certain meeting rooms in an office building, rehearsal or practice spaces in a larger complex, and so on. This is a flexible means of providing access, however the lift for the administrator is also great as employees come, go, and change roles. This is a commonly used access control method for branch security.
- Managed/Mandatory Access Control (MAC): Typically only used in highest-security formats such as government buildings, even administrators do not have the access to change access levels of their teams or subordinates. A MAC is inflexible, but provides the utmost protection.
- Role-based Access Control (RBAC): “In RBAC systems, the owner or system administrator assigns access based on the key holder’s role in the organizations. Everyone has roles and privileges that they are assigned based on their position. Their position also dictates the limitations that will be imposed on them. Access privileges are therefore based on job titles and employment status.”
Wittenbach’s recommended access control products
- DMP control panels: The XR550 is DMP’s flagship model, encapsulating a range of powerful access control capabilities. The panel uses cellular and/or wi-fi network connections to ensure uninterrupted connection to its monitoring center. This panel allows for managing access to specific zones and rooms, flexible scheduling, lockdown mode, and numerous other custom actions that can be tailored to your hours and security needs.
- DMP Virtual Keypad: This nimble remote security solution replaces traditional keypads with ease; its cloud-based application boasts mobile access across zones, buildings, and geographies. Per our recent blog post, user management is another benefit, making access available only to those who should be able to enter and allowing for immediate removal of departed employees. Its reporting features are also auditable, providing real-time status updates of permitted and denied entries.
- Commercial building access: Honeywell offers a suite of different access control products, from control panels to managed access control solutions that allow for locking and unlocking of buildings across geographies. Remote video monitoring also allows for recording of both successful and denied accesses, gracefully preventing unauthorized access.
Access control can be tailored to your branch or business, offering levels of security and user- or role-based entry to control the locking and unlocking of doors and zones. When seeking to upgrade your aging access control system, consider how a mobile, cloud-based virtual keypad can help you achieve this from nearly any device, anywhere. Contact Wittenbach today for best practice advice on purchasing your access control hardware, installation, and maintenance services.